SLA
Terms related to simplyblock
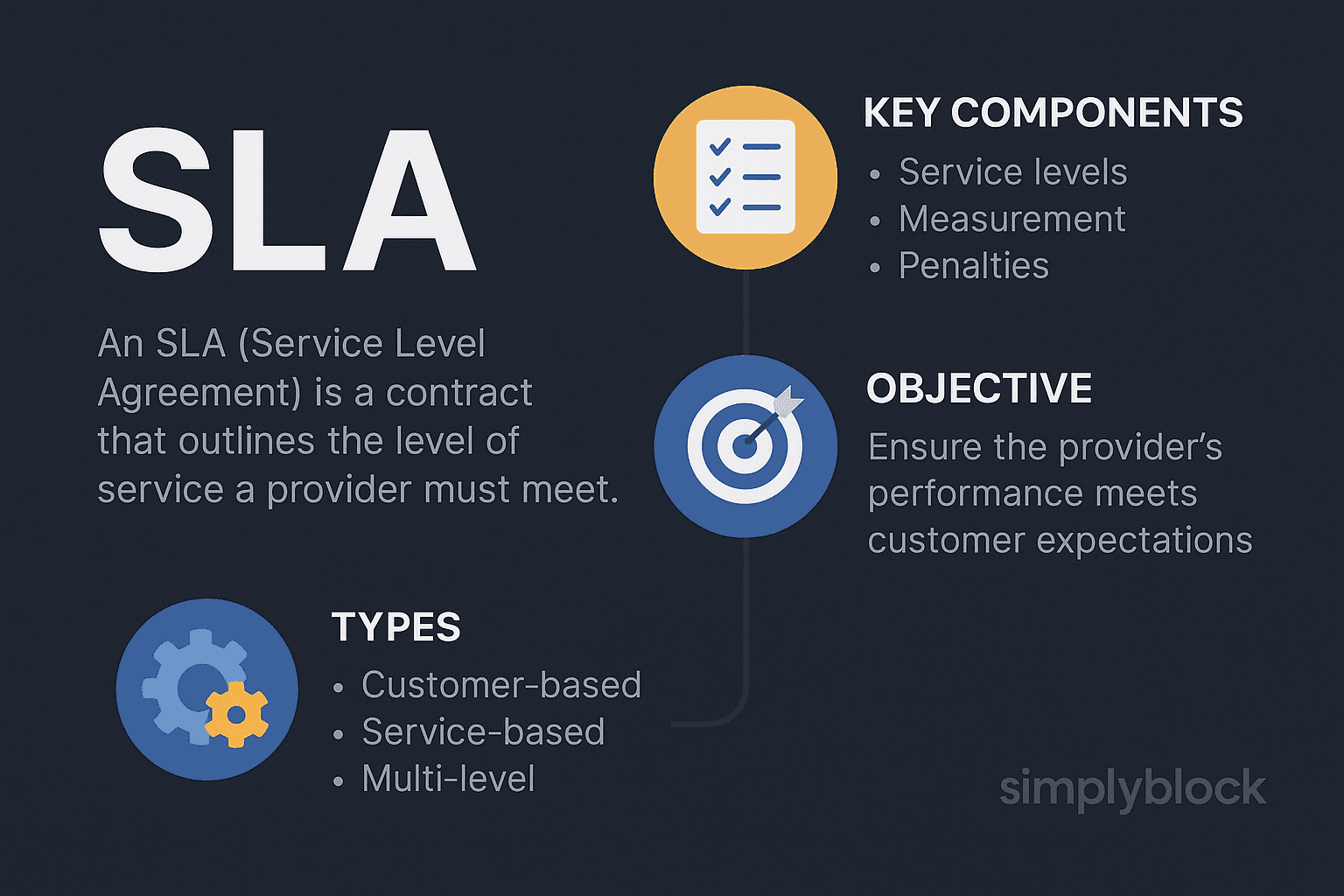
An SLA (Service-Level Agreement) defines measurable service targets, how they are measured, how often they are reported, and what happens when the provider misses the target. In storage, the target set usually covers availability, durability, and performance. Performance commitments often specify percentile latency (p95 or p99), minimum throughput, and sustained IOPS under a stated workload profile.
A storage SLA works only when the agreement ties to clear conditions. Teams should state block size, read/write ratio, queue depth, and the measurement point (client-observed latency versus storage-side telemetry). They should also define exceptions, such as planned maintenance windows, force majeure events, or periods of recovery activity.
For cloud-native environments, the SLA must also align with Kubernetes objects and workflows, so platform teams can enforce it through policy and prove it through repeatable tests.
Production-Grade Ways to Keep Service Targets Enforceable
Teams miss storage targets when they promise “fast” and measure “average.” Percentiles expose user experience, and they show whether the platform protects workloads during contention. Clear reporting windows also matter. Monthly rollups hide short outages that still break customer trust, while minute-level graphs without context create noise.
Software-defined control planes help because they attach performance rules to volumes and tenants. That mapping is foundational for Software-defined Block Storage, where you replace array-wide “best effort” behavior with per-tenant guardrails, clear isolation boundaries, and predictable throughput under mixed workloads. That approach also fits baremetal and virtualized fleets because it standardizes policy rather than hardware.
🚀 Meet SLA Targets Without Complex Manual Ops
Automate SLA delivery with intelligent data tiering, self-healing storage, and scalable Kubernetes-native volumes.
👉 Try Simplyblock for Simplification of Data Management →
SLA in Kubernetes Storage
Kubernetes Storage adds churn by design. Pods reschedule, nodes drain, and clusters scale. A strong SLA survives these events because it ties the promise to the PersistentVolume lifecycle and the CSI workflow, not to a single node. Kubernetes also pushes multi-tenancy into the default architecture, which means one noisy namespace can raise p99 latency for every other tenant if the storage layer lacks hard QoS controls.
To keep the SLA meaningful, define how you measure during rolling upgrades, rebuild activity, snapshot creation, and topology shifts. Then, enforce tenant-level performance policies so one workload cannot spend another workload’s latency budget.
SLA and NVMe/TCP
NVMe/TCP brings NVMe semantics over standard Ethernet, which helps teams standardize on familiar networking while still running NVMe-oF style disaggregated designs. That operational consistency improves the odds that you meet the SLA, because fewer special-case network changes slip into production.
NVMe/TCP alone does not guarantee low tail latency. You still need to manage jitter, queueing, and CPU overhead across initiators, the network, and targets. User-space acceleration, such as SPDK-based IO paths, reduces kernel overhead and helps stabilize latency under concurrency. When the SLA specifies p99 latency, stability matters more than a single peak benchmark.
Measuring and Benchmarking Service Targets
Benchmarks only help when they reflect the SLA conditions. Define the workload profile (block size, mix, queue depth), run long enough to include background activity, and report percentiles instead of averages. Measure from the client side because it reflects the real user experience. Collect storage-side telemetry in the same window so you can explain misses with evidence, not guesses.
In Kubernetes, run tests as Jobs, pin them to nodes, and keep the pod spec stable between runs. Use fio for controlled IO, then track p95/p99 latency alongside throughput and IOPS as a set.
Approaches for Reducing SLA Breaches
Most SLA misses come from variance, not lack of peak performance. These actions reduce variance without adding unnecessary operational overhead:
- Set per-volume limits and reservations, then validate them under intentional noisy-neighbor pressure.
- Keep the IO path short, and avoid extra protocol hops that increase queueing.
- Throttle rebuild, rebalance, and snapshot work so foreground IO keeps its latency budget.
- Use topology-aware placement so volumes avoid cross-zone paths unless the SLA allows it.
- Automate regression tests so each platform change proves it still meets the target.
How Common Platforms Stack Up Against SLA Requirements
The table below focuses on a common SLA requirement: enforceable per-volume guarantees with predictable tail latency in Kubernetes.
| Approach | Enforced per-volume targets | Tail-latency control under contention | Kubernetes alignment | Scaling model |
|---|---|---|---|---|
| Legacy SAN appliance | Limited, often array-wide | Depends on array schedulers | Usually external to CSI workflows | Scale-up silos |
| Public cloud block volumes | Tier-based, opaque internals | Varies with neighbor activity | CSI-friendly, limited visibility | Provider-managed |
| Generic SDS | Possible, tuning-heavy | Depends on IO stack and tuning | Varies by distro | Scale-out, ops-heavy |
| simplyblock | Built-in multi-tenancy and QoS | NVMe-centric, SPDK efficiency focus | Kubernetes-first patterns | Depends on the IO stack and tuning |
Keeping SLA Results Consistent with Simplyblock™ QoS
Simplyblock™ targets predictable outcomes by combining NVMe/TCP with a user-space, SPDK-based IO path that reduces CPU overhead and avoids excess context switching. That architecture helps when your Kubernetes Storage runs mixed tenants and high concurrency, because it reduces the jitter that often drives p99 latency spikes.
Simplyblock also supports flexible deployment models, including disaggregated, hyper-converged, and hybrid layouts, so you can align performance isolation with your risk model. With built-in multi-tenancy and QoS controls, platform teams can set boundaries per tenant and validate compliance through repeatable benchmarking, which keeps SLA reporting defensible.
How NVMe Fabrics Influence Future SLA Targets
Storage contracts are shifting toward percentile-based commitments that match application experience, such as p99 latency and sustained throughput under defined contention. Teams also tighten SLA language around measurement windows and event handling, including upgrades, node drains, and recovery activity in Kubernetes.
More organizations now enforce these targets through policy-driven controls, expressed as code, so platform changes do not weaken performance guarantees without review. Hardware offload via DPUs and IPUs will also matter more as teams push for stable tail latency with lower CPU impact, especially in dense clusters.
Related Terms
Teams often review these glossary pages alongside the Service Level Agreement (SLA) when translating contractual uptime and performance commitments into measurable storage KPIs and operational guardrails.
Network Storage Performance
Storage Latency
SLO (Service Level Objective)
Five Nines Availability
High Availability
External Resources
- Service-Level Agreement – Wikipedia
- Overview of Service-Level Agreements – Microsoft Learn
- SLA Best Practices – AWS Well-Architected
- Google Cloud Platform Service Level Agreements
- Service Level Agreements (SLAs) – IBM Cloud Docs
Questions and Answers
An SLA (Service Level Agreement) defines the expected performance, availability, and support guarantees between a service provider and customer. In storage, SLAs often include uptime guarantees, IOPS targets, and recovery objectives that ensure trust and accountability in cloud-native infrastructure.
Typical SLA metrics include uptime (e.g., 99.99%), latency thresholds, data durability, and recovery time objectives (RTO). High-performance systems, such as NVMe over TCP platforms, often commit to sub-millisecond latency and high availability zones.
In Kubernetes, storage SLAs are tied to the reliability of CSI drivers and the underlying storage system. Kubernetes-native NVMe storage can help meet SLA requirements by delivering fast failover, dynamic provisioning, and consistent performance.
Yes. SLAs may include security guarantees such as encryption at rest and compliance with regulations like GDPR or HIPAA. These commitments are critical in multi-tenant and regulated environments.
SLA violations often trigger penalties such as service credits or contract reassessments. More importantly, they can indicate that your storage solution isn’t delivering the reliability or performance needed, prompting a shift to more robust, software-defined alternatives.
